How to Copy an RFID Card: Tools, Steps & What Can’t Be Cloned
Custom Your RFID Cards
Learning how to copy an RFID card sounds technical, but it’s straightforward for most everyday access cards. This guide covers which cards can be cloned, which tools to buy, the exact steps, and which cards resist duplication.
How to Copy an RFID Card (And Which Ones You Can)
Not every RFID card is copyable. Before buying any hardware, you need to know your card’s frequency.
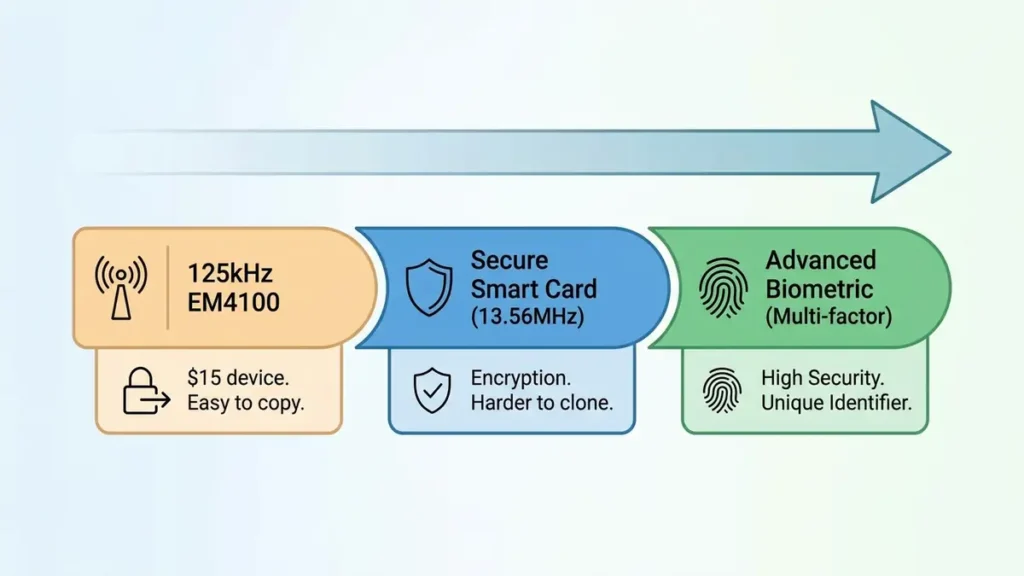
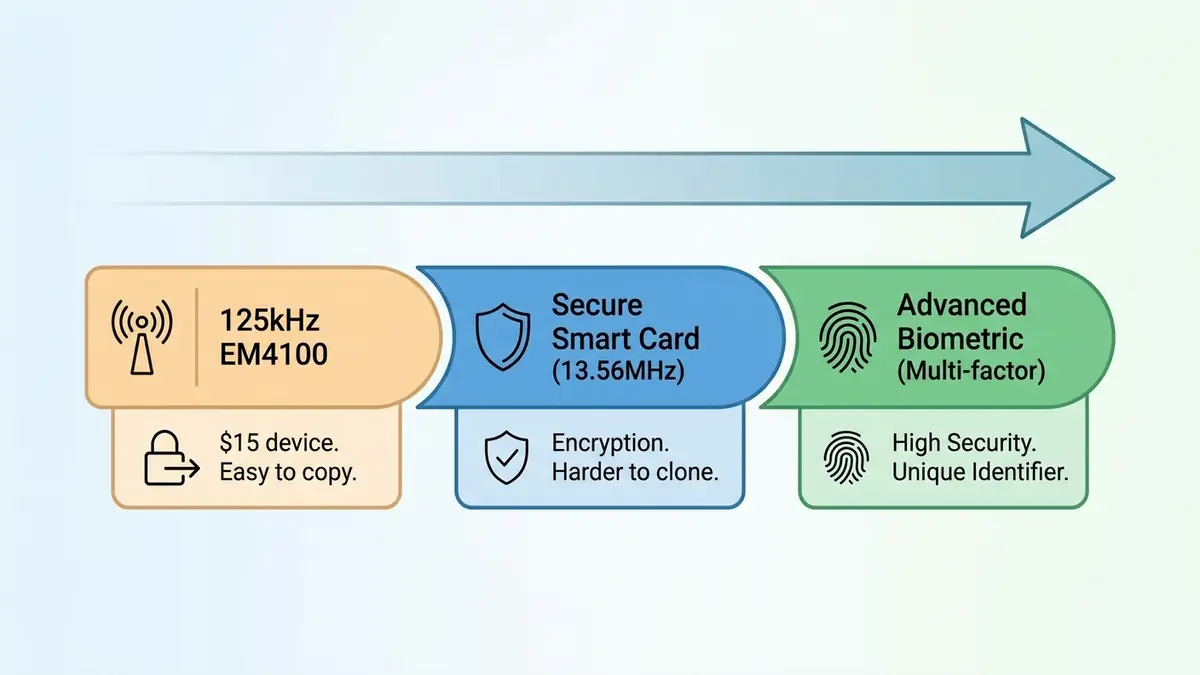
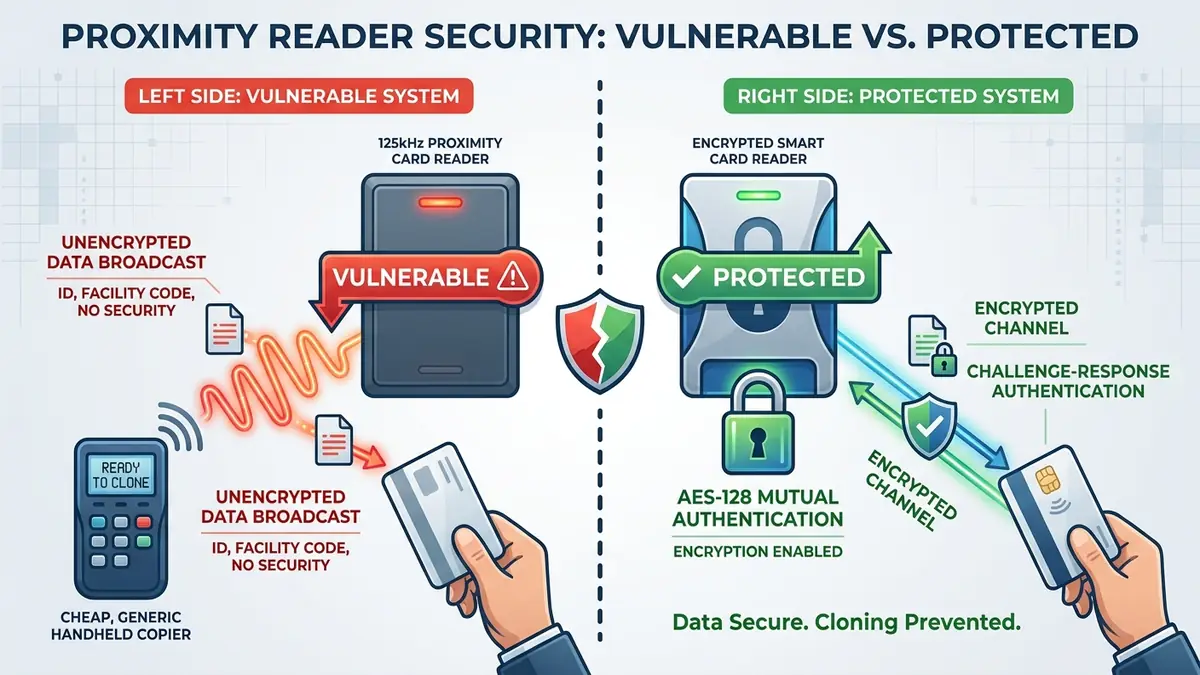
125kHz cards are the easiest to clone. These include EM4100, TK4100, and older HID ProxCard formats. They store a static 26-bit data stream with no encryption at all. Any reader nearby can capture that stream. A $15 handheld duplicator copies them in under 90 seconds.
13.56MHz cards split into two groups. MIFARE Classic and MIFARE Ultralight can be cloned with a multi-frequency copier, because MIFARE Classic uses a broken cipher (Crypto-1, publicly cracked). MIFARE DESFire EV2, DESFire EV3, HID iClass SE, and HID Seos cannot be copied with consumer tools. These use AES-128 mutual authentication: the reader must prove it knows the secret key before the card shares anything. Without that key, no handheld copier can generate a valid response.
One important caveat from security researchers: even a DESFire EV3 card can be effectively bypassed if the access reader is misconfigured to check only the card’s UID. In that case, spoofing the UID grants entry, even without breaking encryption. Proper system configuration matters as much as card technology.
What You Need: RFID Copier Device Comparison
Most people overbuy on hardware. Here’s what each tier actually does.
Budget 125kHz Handheld Copiers ($10-$20)
These devices have two buttons, three LED lights, and run on AAA batteries. Press Read, hold your card, wait for a solid green Pass light. Press Write, hold a blank T5577 fob or card. Done. The T5577 is the universal blank for 125kHz cloning. It works with any budget copier, the XIXEI X7, and the Flipper Zero.
The limitation is firm: these devices do not work at 13.56MHz. Holding a MIFARE card to the sensor shows only a blinking “Busy” light.
Multi-Frequency Copiers like the XIXEI X7 ($40-$60)
The XIXEI X7 covers both 125kHz and 13.56MHz. Auto-detects frequency on a 2.8-inch color display, charges via USB-C, and holds charge through 50 or more sessions.
For 13.56MHz cards, you need the right blank. UID Gen 1 cards work on most readers. CUID (Gen 2) cards work on readers that reject Gen 1 magic cards. A Windows PC app handles more advanced MIFARE Classic decryption with default keys.
Flipper Zero (~$169)
The Flipper Zero supports RFID, NFC, Sub-GHz, and infrared in a pocketable device. For RFID copying, it silently reads a 125kHz card in under one second, through a wallet or jacket pocket. It stores the data and emulates the card at any compatible reader. The Flipper cannot break DESFire EV2/EV3 encryption, but for 125kHz and basic 13.56MHz cards, it’s the most convenient tool available.
| Device | 125kHz | 13.56MHz | Encrypted Cards | Price |
|---|---|---|---|---|
| Budget handheld | Yes | No | No | $10-$20 |
| XIXEI X7 | Yes | Yes (most) | MIFARE Classic only | $40-$60 |
| Flipper Zero | Yes | Yes (basic) | No | ~$169 |
The blank cards you’ll need are T5577 RFID cards for 125kHz cloning, and UID or CUID cards for MIFARE Classic 1K frequency systems.

Step-by-Step: Copying a 125kHz Card
This is the process for the most common type of RFID card in gyms, offices, and apartment buildings.
Reading the Original Card
- Insert two AAA batteries and power on the device
- Hold your original card flat against the sensor
- Press Read and wait for a solid (not blinking) Pass light
- Blinking or Busy-only means the card is not 125kHz EM4100. Stop and check your card type.
If the Pass light blinks, reposition slightly closer to center and retry. The sensor location varies by model.
Writing to a Blank T5577 Card
Keep the device on with the Pass light still solid. Data stays in memory until you write or power off.
- Hold a blank T5577 fob or card to the sensor
- Press Write and wait for a second Pass confirmation
- Test the clone on the original reader
If it fails, re-read and re-write. Budget devices sometimes need two or three attempts to write consistently.
Common Failure Points
The most common mistake is using the wrong blank card. T5577 is specifically required for 125kHz cloning. A regular MIFARE card will not accept 125kHz data. The second most common issue: blank T5577 cards have no data, so they show no Pass light when read. Test only after writing.
Copy an RFID Card to Your Phone
Android phones with NFC hardware can read and write 13.56MHz NFC tags using apps like NFC Tools or MIFARE Classic Tool. Android’s Host Card Emulation (HCE) even lets the phone act as a cloned card at a compatible reader, for basic unencrypted NFC tags.
iPhone is more restricted. Apple allows reading NFC tags since iPhone 7, but blocks open emulation for third-party apps. You can store passes in Apple Wallet for transit and hotel access only when the issuer officially supports it. Freely emulating arbitrary RFID cards is not possible on iPhone.
Neither Android nor iPhone works with 125kHz cards. Smartphone NFC hardware operates only at 13.56MHz. If your fob is 125kHz, a handheld copier is the only consumer option. Understanding HF RFID vs NFC differences clarifies which phone apps apply to your card type.
The NFC tag types guide covers NTAG, MIFARE, and NFC standards in practical depth.
Security and Legal Considerations
Copying a card you own or are authorized to use is generally legal in the US, UK, and Australia. Using a clone to access a location you’re not permitted to enter is criminal: it triggers computer fraud, trespass, and unauthorized access statutes across all three jurisdictions. Copying someone else’s card without permission is also illegal regardless of intent.
On the defense side, organizations still running 125kHz proximity systems remain fully exposed. A $15 device and a $2 blank card are all an attacker needs. The upgrade path runs from 125kHz proximity cards to MIFARE Classic (marginal improvement, as Crypto-1 is broken) to DESFire EV2/EV3 or HID Seos. Those systems use AES-128 challenge-response authentication plus anti-replay session tokens, making them resistant to all consumer cloning tools available today.
Black Hills Information Security’s RFID proximity cloning research documents these attacks in detail, including why legacy systems stay vulnerable years after the weaknesses were first published.
If you manage an access control system, reviewing your current card types against the dual-frequency RFID card options and encrypted alternatives is a practical starting point.
What to Do Next
Most apartment fobs and gym key cards use 125kHz EM4100 format. A $15-$30 handheld copier handles them in under two minutes. For 13.56MHz cards, a multi-frequency device like the XIXEI X7 covers most non-encrypted formats. DESFire EV3 and iClass SE cards cannot be copied with any consumer device today. If you manage a building’s access system, that last category is where your upgrade path leads.
How to Copy an RFID Card FAQs
Can I copy any RFID card with a cheap duplicator?
No. Budget duplicators work only with unencrypted 125kHz cards like EM4100 and TK4100. DESFire EV2/EV3 and iClass SE use AES-128 encryption with mutual authentication. No consumer device can clone them.
Is copying an RFID card illegal?
Copying a card you own or are authorized to use is generally legal in the US, UK, and Australia. Using a clone to enter somewhere you’re not permitted is a criminal offense. Copying another person’s card without permission is also illegal.
What blank cards do I need for RFID cloning?
For 125kHz cards: T5577 fobs or cards. For 13.56MHz MIFARE: UID Gen 1 or CUID Gen 2 blanks, depending on whether your reader checks for magic-card markers.
Can my Android phone copy an RFID key fob?
Android can read and emulate basic 13.56MHz NFC cards using NFC Tools or MIFARE Classic Tool. It cannot copy 125kHz fobs. Encrypted cards (DESFire EV2+, iClass SE) block phone-based copying regardless of the app.