Decoding EPC Gen 2 V2: The Protocol for High-Speed, Secure UHF RFID
Custom Your RFID Cards
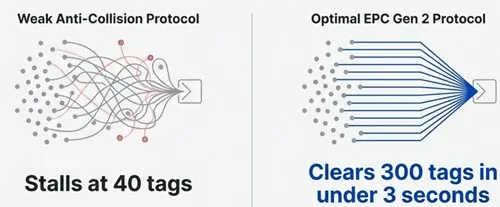
Last post we showed that UHF dominates bulk inventory because it balances range, speed, and cost. But frequency is only step one. The real differentiator lies in the protocol running on that band. A 915 MHz reader with a weak anti-collision algorithm may stall at 40 RFID tags. Another, using EPC Gen 2 optimally, clears 300 RFID tags in under 3 seconds. Same spectrum. Different protocol execution. EPC Gen 2 is not optional infrastructure. It is the foundation of global UHF RFID interoperability. Gen 2 V2 extends that foundation with authentication, access control, and privacy which is critical for regulated supply chains. This article will show you how the Q-algorithm delivers real-world throughput, how V2 secures data at the air interface, and what to verify before deployment. Because in UHF, the protocol is the product.
Part 1: Protocol Genesis: Why UHF Needed a Universal Language
1.1 The Core Bottleneck in Modern Supply Chains
RFID deployment in logistics and retail must support reliable reads from 1 meter to 10 meters while processing hundreds of tags per second. Barcodes and older RFID protocols cannot meet this bulk reading requirement. The limitation is not antenna gain or reader power. It lies in the lack of deterministic singulation at the protocol level. Without it, RFID remains a niche tool.
1.2 Protocol Identity: EPC Gen 2 and ISO 18000-63 Are Technically Identical but Governed Separately
EPC Gen 2, defined by GS1 and EPCglobal, and ISO/IEC 18000-63, published by the International Organization for Standardization, specify the same air interface. Their divergence is functional, not technical. ISO/IEC 18000-63 ensures hardware interoperability across borders. It mandates compliance with regional RF regulations and guarantees that tags and readers from different vendors can communicate at the physical layer. EPCglobal defines the data layer. This includes the Electronic Product Code format, memory bank organization, and application-level rules for data sharing. It enables a pallet tagged in Shanghai to be read, interpreted, and acted upon in Rotterdam. Together, they form a complete stack: ISO for connectivity, GS1 for commerce.

1.3 Physics Alone Does Not Deliver Performance
UHF frequencies enable longer range and faster data rates than LF or HF systems. Yet raw spectrum advantage is wasted without intelligent protocol control. Gen 2 turns physics into productivity through precise timing, adaptive arbitration, and power negotiation.
Part 2: Core Mechanism: The Q-Algorithm and High-Speed Singulation
2.1 Collisions Are Inevitable in Dense Tag Populations
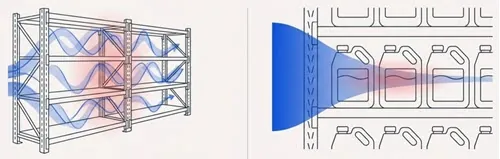
A UHF reader’s field can energize dozens or hundreds of tags simultaneously. If multiple tags transmit at once, their backscattered signals interfere, corrupting the reader’s receive path. Collision resolution is the protocol’s primary function.

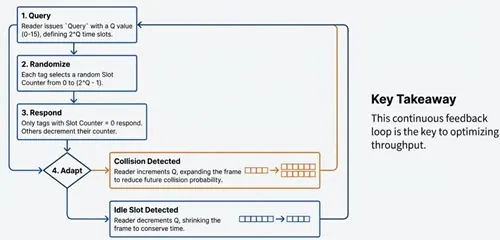
2.2 The Q-Algorithm Executes Adaptive Slotted ALOHA
Singulation in Gen 2 uses a dynamic frame-slotted ALOHA approach governed by the Q parameter. The reader sends a Query command with a Q value from 0 to 15. This defines a frame of 2^Q time slots. Each tag draws a random integer, the Slot Counter, from 0 to 2^Q minus 1. Only tags with Slot Counter equal to 0 respond in the current slot. All other tags decrement their counter after each slot. Crucially, Q is adjusted in real time. If two or more tags respond in one slot, a collision occurs and the reader increments Q. This expands the frame, reducing collision probability. If no tag responds, the slot is idle and the reader decrements Q. This shrinks the frame, conserving time and boosting throughput. This feedback loop achieves over 90 percent channel efficiency in practice. Legacy static protocols rarely exceed 35 percent.
2.3 Real-World Throughput Gains Are Measurable
A Gen 2 reader can inventory a full pallet of 200 tags in under 2 seconds at a dock door. Handheld inventory of a retail shelf drops from 5 minutes to 15 seconds. These improvements stem from algorithmic efficiency, not increased transmit power.
Part 3: Evolution to Gen 2 V2: Security Built Into the Air Interface
3.1 Speed Is Necessary but No Longer Sufficient
Gen 2 solved inventory speed. Gen 2 V2, ratified in 2015, solves trust. As RFID enters pharmaceuticals, defense, and luxury goods, unprotected tags invite counterfeiting, diversion, and data tampering. V2 embeds security directly into the tag-reader handshake.

3.2 Three Protocol-Level Security Features Define V2
Tag Authentication enables cryptographic verification of tag identity. A reader issues a challenge. The tag computes a response using a pre-shared secret, typically via AES-128. Counterfeit tags that copy memory but lack the key fail immediately. Data Access Control is granular. Memory banks such as EPC, TID, and User can be locked individually. V2 adds Permalock, which permanently protects selected bits. Separate access and kill passwords remain supported. BlockWrite permissions allow selective write enablement. Privacy Protection includes Silent Mode. On command, a tag stops broadcasting its EPC until reactivated. This satisfies regulatory requirements for consumer data minimization without requiring permanent deactivation.

3.3 Industry Adoption Reflects Tangible Risk Reduction
Pharmaceutical manufacturers use V2 to comply with the U.S. Drug Supply Chain Security Act. Each serialized unit is cryptographically bound to its pedigree. Luxury brands authenticate high-value items at point of sale to deter gray market diversion. Aerospace suppliers use Permalock to protect maintenance logs embedded in tool and component tags. Security is now part of the standard. It is not optional.
Part 4: Environmental and Regulatory Constraints
4.1 Real-World Performance Is Governed by Physics
Most field failures trace to environmental factors, not protocol defects. Metal reflects UHF signals and detunes tag antennas. This creates localized null zones where coupling efficiency drops by 20 dB or more. Liquids, particularly water, absorb UHF energy. A bottle of saline solution can reduce read range by 70 percent over a short path. These effects are well understood. They require engineering responses, not protocol revisions.
In fact, there are UHF anti-metal RFID tags and anti-liquid RFID tags for using in these environments.
4.2 Solutions Must Remain Fully Compliant
On-metal applications demand specialized tags. These use ferrite shielding, shorted patches, or near-field coupling to restore performance. All must still pass ISO/IEC 18000-63 conformance testing. Liquid-rich environments call for impedance-matched antennas with detuned resonance. Again, compliance is non-negotiable. Global frequency allocation varies. North America uses 902 to 928 MHz. Europe uses 865 to 868 MHz. Japan uses 952 to 954 MHz. Gen 2 requires readers to support region-specific hopping sequences, dwell times, and output power limits. A compliant reader adapts to local rules via configuration, not firmware replacement. Regulatory compliance is binary. Either a product meets the standard, or it does not.
Part 5: Conclusion: The Protocol Is the Foundation
UHF RFID’s value in global supply chains is not about maximum read range. It is about predictable, secure, high-volume identification. That capability exists because of deliberate protocol design. A reader claiming 15-meter range but stalling at 60 tags is inferior to one reading 8 meters reliably at 300 tags per second. A tag with 512 bits of user memory but no V2 authentication is a liability in regulated industries.
Procurement decisions should focus on three verifiable criteria:
- Demonstrated Q-adaptation performance under high tag density
- Certification to EPC Gen 2 V2 and ISO/IEC 18000-63:2023
- Native support for Tag Authentication, Permalock, and Silent Mode without proprietary extensions
The protocol is the invariant. Everything else is implementation detail.
Deploy with Confidence
Specify only EPC Gen 2 V2 certified tags and ISO 18000-63 compliant readers. Ensure your solution delivers the protocol’s full promise: subsecond bulk reads, cryptographic trust, and global regulatory readiness. That is how modern supply chains achieve velocity, visibility, and integrity. That is the standard.
EPC Gen2, standardized as ISO/IEC 18000-63, plays a central role in modern UHF RFID systems. To understand how it fits into the broader RFID standards ecosystem, see our RFID standards guide .